What are quantum computing and quantum communication?
Share this Post
As far as technology hype cycles go, ‘quantum’ is on its way to quickly outpacing prolific buzzwords such as ‘artificial intelligence’ and ‘machine learning.’ There is no shortage of enthusiastic articles claiming, for instance, that scientists have found an ‘angel particle’ that will make our computers 100 million times faster. Other sources falsely suggest that quantum communication will enable clever engineers to build “unhackable networks that transfer data faster than the speed of light,” which would amount to an impossible violation of the laws of physics. For Scott Aaronson, one of the world’s leading quantum computer scientists, the field is now so “awash in venture capital and large investments from governments and corporations” that the explosion of interest in quantum computing has engendered a lot of confusion and misperceptions about key concepts.
In the years to come, quantum technologies will be playing an increasingly important role in how we do computing, communicate, secure our critical national infrastructure, and even engage in armed conflict. That’s why it’s important to know how to distinguish between hype and accurate reporting about this new age of quantum, and to develop a basic understanding of both the potential and the challenges of quantum technologies so that we can form rational expectations and draft sound regulatory policies. Outlining some of the key issues at stake is what this Explainer seeks out to do.
Background
Today’s best supercomputers are immensely powerful. The UK Met Office’s Cray XC40, for instance, runs 14,000 trillion arithmetic operations per second to forecast weather changes. However, there are some important problems in nature and society that are too complex for even our best digital supercomputers to handle. Or sometimes, the nature of the problem is such that it can’t be solved within a workable timeframe. For instance, a digital computer finds it very difficult to work out the two large prime numbers P and Q, of which a super large integer N is the product. If P and Q are given, it’s easy to work out N = P x Q. However, working backwards, i.e. finding P and Q for a given N is much more difficult. This is called the factoring problem, and the slowness of digital computers when it comes to factoring large numbers is exploited in RSA encryption, which secures most of our online communication today.
Quantum phenomena are also difficult to model. This is because the number of possible states into which a quantum system can evolve quickly grows in complexity to a degree that completely overwhelms a regular digital computer. The potentially improved modeling of quantum effects holds big promises for research in mathematics, physics, astronomy, chemistry, logistics, and finance to name but a few – problems that currently are just too big for standard computers to solve. In 1982, star physicist Richard P. Feynman proposed a seemingly simple yet revolutionary idea: Why not build a quantum computer to solve quantum problems? Surely, a machine that resembles in kind the problems it is supposed to solve can only be more effective.
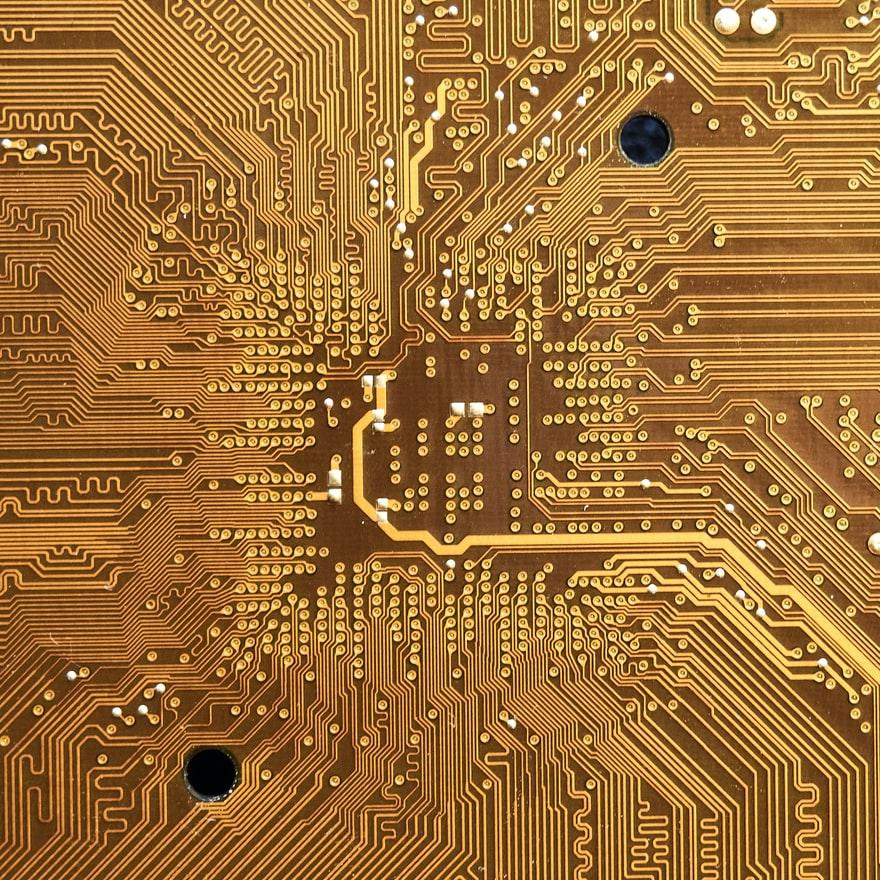
In the years that followed, the potential of quantum computers to outperform classical machines in important areas was demonstrated fairly swiftly – at least in theoretical terms. In 1994, Peter Shor showed that a quantum computer could indeed tackle the factoring problem efficiently and therefore would be able to crack the above-mentioned protocol that makes our online traffic safe – a considerable threat to global cybersecurity. All that was left to do, theoretical computer scientists argued back then, was to simply build such a machine – but this proved massively more difficult to do in practice than anticipated conceptually. Curiously, then, in terms of concept and idea, the quantum computer is already 40 years old even though we’re still waiting for a proper fault-tolerant machine to enter the scene. Only thanks to substantial recent progress in optoelectronics, materials science and engineering, making it possible to create the hardware that’s required to house quantum circuits, has it been possible to actually build elementary parts of this new type of computer.
But what is a quantum computer, exactly?
Quantum computing invites us to radically rethink how computing works. In classical digital computing, e.g. the laptop or smart device on which you’re reading this article, the basic computational unit is a bit. A bit represents the actual mechanics of computational processes. Modern computers contain millions if not billions of tiny transistors to which voltage can be applied. If applied, a transistor conducts a current. This state is usually represented by the digit 1. When no voltage is applied, the system is off, represented by the digit 0.
By chaining many transistors together and applying voltage selectively, complex gates can be created that generate large strings of 0s and 1s, which, in turn, represent data such as letters and numbers. Alternately, the electric charge changes the polarization of liquid LCD crystals so that they change color, which creates a moving image on a laptop screen. The bit is binary because it can only ever be in one of the two states described: either a current is flowing or it is not. Whenever the bit is not 0 it must be 1 and vice versa. A classical bit can never be in both states at the same time. By way of illustration, your kitchen lights at home are either switched on or they’re switched off. Surely, they can’t be both on and off, at least not at exactly the same moment in time.
The picture is a radically different one in the world of quantum computing. Here, the basic unit is called a quantum bit, or qubit. There are several candidates for such qubits, and many engineering approaches compete in this space. Superconducting circuits, trapped ions, neutral atoms and even photons all qualify for the job. These qubits can be manipulated in such a way so that they’re not just 0 or 1, but in a state somewhere in between. Colloquially speaking, a qubit can be in two states at the same time, where it is at once “some percentage” 0 and “some percentage” 1. Qubits are Schrödinger’s proverbial cat; they are at once dead and alive. This state is called the superposition state. While perhaps counterintuitive at the first encounter, it is a fundamental principle of quantum physics.
But that is not all. Two such qubits can be manipulated to form a special kind of relationship with one another that physicists call entanglement, so that the state space is shared across both qubits. This has radical consequences for the concept of computing. While a single qubit can hold 21 = 2 states, an entangled pair of two qubits can hold 22 = 4 different states, 3 qubits manage to hold 23 = 8 states and so forth. A machine with n qubits can therefore hold 2n states at the same time, and each state represents a computational operation.
A theoretical quantum computer with 300 logical qubits that all work reliably would therefore be able to hold 2300 states at the same time, which means it could perform 2300 operations simultaneously. This is an unimaginably vast figure – scientists estimate that the number of all sub-particles in the entire visible universe is 2300; hence, this figure is an illustrative example of the enormous magnitude of the promises that quantum computing holds. While it must be said that such a powerful machine is unlikely to ever be built, even a much less colossal machine would mean an enormous scale up of computational resources. This promise has motivated private corporations and state actors to scramble to be the first to build a computer of this kind. With so much at stake, no actor can afford to come in second in the newly emerging quantum race.
What’s the current level of development?
Critics of the quantum computing paradigm have been joking for a long time that for decades, when asked at what point a quantum computer will finally become available, quantum evangelists have consistently responded that they’re less than 10 years away from a working model.
But this picture has changed, thanks to vast improvements in auxiliary technologies that are required to build quantum machines. Several comprehensive if not exhaustive lists of private corporations that are involved in quantum computing circulate online, and contain all the usual suspects, including IBM, Alphabet (the proprietor of Google), Microsoft, Alibaba, Toshiba and D-Wave. Many start-ups have been founded as well.
Out of all competing modalities, at this point, superconducting qubits seem the most promising approach to quantum computing. Google and IBM have been vying with competing claims as to who is doing better, with IBM publicly doubting Google’s 2019 declaration of “quantum supremacy,” i.e. the point where a quantum computer outperforms the fastest available digital system on a well-defined (if not necessarily useful) task. Microsoft, on the other hand, has been pursuing a radically different path, but recently had to admit that they overstated the level of progress they’d been making with their approach based on Majorana particles.
While incredible achievements have been made over the past couple of years, many problems remain. The most pressing ones revolve around decoherence, i.e. the inevitable, gradual loss of signal quality in real-world environments, and error correction. It’s no easy task to keep qubits stable and steady long enough to perform meaningful computations; by their very nature they decohere very quickly (hence the massive cooling effort to arrest them as much as possible). Then there is computational noise and plenty of errors that occur in the system. An obvious solution to this problem is to include more qubits so that they can ‘jump in’ and replace faulty ones. Estimates suggest that for a basic standalone quantum machine to run properly, it would need to hold around 1,000 qubits. That means there’s a long way to go, given that experimental computers currently average around 60 qubits. Error correction remains the single biggest obstacle to realizing the goal of a standalone quantum computer.
It’s also important to note contrary to the media hype, a quantum computer will be a specialized machine that will be incredibly better at some known (and many new) problems, but not universally faster for each and every computing task. Early machines are likely to be the size of a family home, consume vast amounts of energy for cooling down qubits to almost absolute zero, and likely require protection by security teams – all of which comes with huge costs, such that these early machines are likely to be deployed primarily by government or research organizations; we won’t be tweeting from a quantum smartphone any time soon.
Early applications: quantum communication
Because large-scale, fault-tolerant quantum computers are so notoriously difficult to build, it makes sense to build smaller devices and connect them over the cloud to provide entanglement at scale. The field of quantum communication is concerned with developing secure quantum channels for this purpose, and for secure communication generally. Quantum Key Distribution, or QKD, is one of the most researched topics in this field. QKD exploits the phenomenon of quantum teleportation to generate key pairs that allow for the encryption and decryption of messages.
Due to its name, this research area is significantly misperceived among parts of the public, who associate it with the fictional Star-Trek device that could beam solid matter from one place to another. Teleportation in the context of quantum communication means that due to the nature of entangled particles in the superposition state, it is possible to take the measurement of an available qubit in order to reveal the state of another. To paraphrase: quantum teleportation enables researchers to measure a qubit in their lab, and thereby to instantaneously reveal, to the same researchers, the measurement of a qubit in a different place (that is very distant , theoretically, even at the other end of the universe). This happens instantaneously. Since we do not know of any mechanism that would allow any particle to travel faster than the speed of light, it is impossible for any information to quickly travel from one place to the other. This is certainly a curious property of qubits. Albert Einstein, who’d initially been doubtful about teleportation, dismissed the phenomenon as “spooky action in the distance, ” but later accepted the phenomenon is real.
Putting this admittedly weird principle to work, scientists can build a secure quantum channel that exploits the teleportation phenomenon. Any eavesdropping activity would disturb the intricate relationships among the qubits involved, which would be noticed by the sender and receiver of the message so secured, and then communication would be aborted. While quantum hackers have successfully exploited hardware weaknesses, in particular at the endpoints of quantum channels that integrate with legacy communication systems, the qubit mechanism is secured by the laws of physics and is therefore in principle, if not in reality, impenetrably secure.
Early applications of new quantum technologies, before quantum computers become market-ready, will be in the domain of quantum-secured communication. Secure cloud computing and truly random number generation, which is hugely important for many scientific as well as commercial applications, is another profitable application. While the science behind quantum technologies has surely made quantum leaps over the past two decades, the commercialization of quantum will be a stepwise introduction and integration with existing legacy infrastructure.
Looking ahead: When global powers go quantum
In a world of intensifying competition between the US and China and an increasingly multi-polar world, quantum computing sits at the forefront of the geopolitical concerns of strategists on both sides of any conflict. China is keen to develop a genuinely Chinese technology in this space that is not subject to technology transfers from the West. As far as quantum communication is concerned, the Chinese government made explicit their ambitions for a leadership position in 2016 when it launched the world’s first quantum satellite that shoots entangled particles across vast distances. Error-prone as it may be, Micius is a strong signal that China must be considered a leading player in the quantum game.
Since then, the US has stepped up its efforts, and so has Europe. The chief worry among cybersecurity strategists is to prepare for a case where an adversary would get its hands on a rudimentary quantum machine while also being able to secure its own communication over quantum channels. Considerable efforts are currently underway to standardize encryption protocols that can hold up against the vast computational resources that quantum machines will offer. This field is known as post-quantum cryptography; it is one of the most important cybersecurity challenges of this day. Even if a truly useful quantum computer is still 10 years away, in many instances governments must keep sensitive material classified for three decades or more, which has made the problem of quantum hacking an urgent matter well before any viable quantum computer has arrived on the scene. Even if quantum computing is unlikely to deliver on its big promise to revolutionize computing, no government can afford to take any chances.
Further Reading
Aron, Jacob. “Quantum Internet Goes the Distance.” New Scientist 238, no. 3177 (May 9, 2018): 13.
Bokulich, Alisa, and Gregg Jaeger, eds. Philosophy of Quantum Information and Entanglement. Cambridge University Press, 2010.
Bruss, Dagmar, and Gerd Leuchs. Quantum Information: From Foundations to Quantum Technology Applications. 2 volume set. Wiley VCH, 2019.
Castelvecchi, Davide. “The Quantum Internet Has Arrived (and It Hasn’t).” Nature, February 14, 2018. https://doi.org/10.1038/d41586-018-01835-3.
Costello, John K, and Elsa B. Kania. “Quantum Hegemony: China’s Ambitions and the Challenge to U.S. Innovation Leadership.” Technology & National Security. Washington DC: Center for a New American Security, 2018.
Kashefi, Elham, and Petros Wallden. “Cyber Security in the Quantum Era.” Communications of the ACM 62, no. 4 (April 2019): 120–29. https://cacm.acm.org/magazines/2019/4/235578-cyber-security-in-the-quantum-era/fulltext.
Kimble, H. J. “The Quantum Internet.” Nature 453, no. 7198 (June 2008): 1023–30. https://doi.org/10.1038/nature07127.
Nielsen, Michael A., and Isaac L. Chuang. Quantum Computation and Quantum Information: 10th Anniversary Edition. 10th Anniversary edition. Cambridge, New York: Cambridge University Press, 2010
This Explainer is published as part of the German-Israeli Tech Policy Dialog Platform, a collaboration between the Israel Public Policy Institute (IPPI) and the Heinrich Böll Foundation.
The opinions expressed in this text are solely that of the author/s and do not necessarily reflect the views of the Israel Public Policy Institute (IPPI) and/or the Heinrich Böll Foundation.
Share this Post

Weaponizing Bots and Data: The Brazilian Electoral Experience of 2018
In recent years, political parties and campaigners around the world have invested heavily in online advertising, demonstrating the…

Covid-19 Vaccine Passports and Their Impact on Privacy and Autonomy
Authors: Oskar J. Gstrein and Dimitry Vladimirovich Kochenov While most regions of the world are still struggling to get their hands…
How does Germany's Traffic Light coalition plan to accelerate the country's energy transition?
Germany has ambitious targets to drastically cut its greenhouse gas emissions in the coming years and to achieve…
